Why CISOs need to hire data security experts & what to look for
November 1, 2023 | 8 min. read

Data is more critical than ever in 2023. It fuels innovation, powers business growth, and can even be monetized. In many ways, it’s even comparable to uranium or oil! But, many organizations haven’t yet focused on protecting it to the extent that its value deserves and requires.
Even if teams are actively seeking to improve their data security, it’s challenging to do so within today’s multi-cloud environments. Cloud storage makes it easy for developers and data scientists to move, modify, or duplicate sensitive data in seconds. This proliferation of data means that data security is much more challenging than it used to be in the days of only on-premises storage.
But just because something is difficult doesn’t mean it shouldn’t be handled head-on. Failing to protect or manage data as it proliferates often leads to adverse outcomes. A successful data breach can lead to irreparable damage and adverse outcomes like customer churn, negative public sentiment, CISO turnover, and increased regulatory scrutiny. In addition, because cloud providers price their storage as a service, it costs money for unknown, unused data to just sit inside cloud stores.

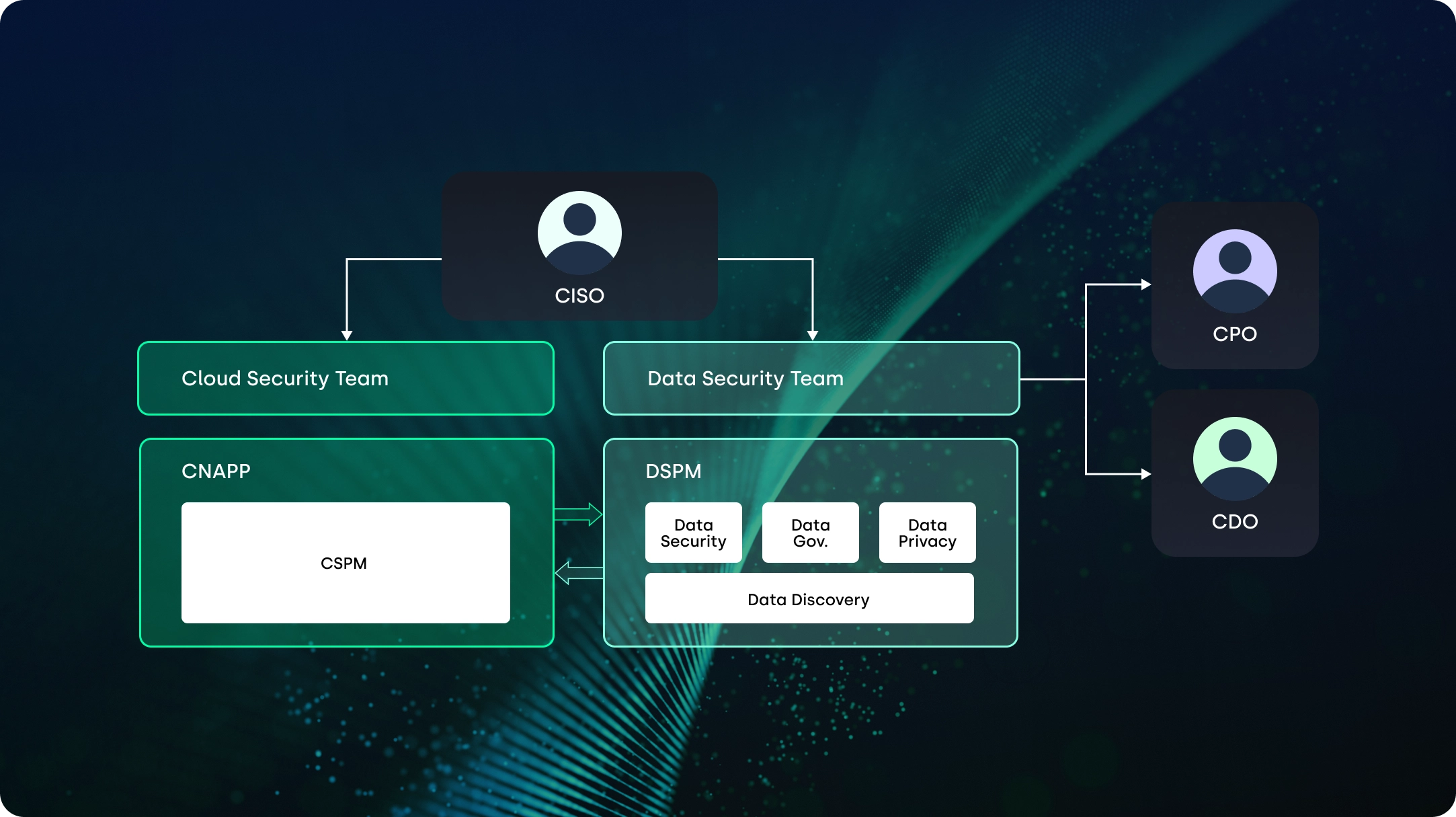
One of the key elements to successfully implementing data security in the cloud is finding the right person (or people) to head up the process. Because data is an invaluable resource for today’s businesses, CISOs need to consider data security a separate practice from their other security disciplines.
Once they have decided to hire for the function of data security, what this looks like in practice depends very much on the size of the organization. It could be a center of excellence (COE) within a large enterprise, a smaller data security team at a medium-sized enterprise, or one dedicated professional for smaller organizations. But whatever it looks like, if you haven’t built a team of data security experts yet, the time is now!
Despite how critical data is to the business, historically organizations have sidelined data security as a discipline, grouping it with other security practices. If a company does have dedicated data security personnel, often they reside in an entirely different team (e.g., privacy and compliance).
Because many organizations think of data security as a privacy and compliance function, they may assume that “bare minimum” standards are enough. But even if your data assets met compliance standards six months ago, that doesn’t mean your data isn’t exposed today! The static/point-in-time documents that auditors rely on don’t match the dynamic nature of data and associated risks in today’s cloud environments.
This lack of focus on data security and adequate tooling means many teams don’t know where their data resides, which team members or third parties can access it, and how to protect it. The scope of this problem was highlighted in our State of Cloud Data Security Report 2023, in which 77% of participants said they had experienced a public cloud data breach in the last year.
Instead, data security in today’s world requires a more in-depth, continual, and agile approach. It must focus on maintaining data visibility, monitoring and controlling access, enforcing policies, and protecting data across an ephemeral attack surface.
These new demands have created a growing data security skill gap: the need for a qualified data security professional or team reporting to the CISO.
Ideally, this data security expert (or team) would focus solely on securing sensitive data across the organization. They would mainly focus on four areas:
The data security expert will be a business enabler, working with the Chief Data Officer (CDO) to optimize data security processes and tools across teams and the Chief Privacy Officer (CPO) to help them meet regulatory requirements.
When hiring a data security expert, look for professionals with these things on their resume:
Even knowing that we are in the midst of a prolonged security skills shortage, it’s important to hire the right person or team as your trusted data security expert(s). They will be responsible for keeping the organization’s most sensitive data safe, empowering its data users, and fulfilling the operational needs of security’s counterparts in the governance, privacy, and compliance organizations. That’s why as they search for this “data security expert” or team, CISOs should look for a few specific characteristics. These include:
As we’ve mentioned, data security in the cloud takes an entirely different mentality than traditional on-premise security. Sensitive data doesn’t just live inside known data stores. It also ends up in temporary backups, versions believed deleted, state files, undocumented S3 buckets, and more. It exists in an entirely different set of technologies, and understanding and protecting that data requires completely different expertise from on-premises data security. The best data security experts understand how both types of storage work so they can work well with the ephemeral nature of cloud data and the sprawling nature of cloud technologies as well as the legacy data their organizations choose to keep on-prem. Bonus: The data security expert should also have experience in standard data security techniques such as encryption and tokenization.
It’s the data security professional’s responsibility to translate data laws and governance best practices into requirements that can be operationalized by their peers in GRC and privacy.. While an understanding of the nuances of every regulation isn’t required, overall understanding of the regulatory landscape that applies to their organization is critical.
From the MITRE ATT&CK to Cloud Data Management Capability (CDMC)—there’s a framework for that. Because there are several helpful data security frameworks that implement a common language and provide a structure for data protection processes and controls, it’s recommended that the data security expert understand how to implement such a framework.
The data security expert must understand how the business, including the supply chain, works. To evaluate data security they need to understand who should and should not have access to what data, whether they’re suppliers, other third parties, or employees across the organization. They need to understand and get to know their peers in the developer and data science organizations, as well as their motivations, so they understand their motivations and can truly be business enablers.
They also need to know how different security teams work within other business units, such as application development, cloud infrastructure, etc. so that if something does go wrong, they need to know how to respond and work with the rest of the security team to remediate the issues.
Qualified data security professionals can communicate clearly with all stakeholders: the c-suite, as well as privacy, governance, and compliance. It also helps if they have a high level of diplomacy when working alongside IT personnel, developers, data scientists, etc., and their different priorities. Developer and data science teams usually own the cloud technologies that contain data, so they must be involved in remediation. Similarly, IT must be involved in remediating on-premises data exposures.
Your data security expert’s efforts must also align with the overall data pipeline used across the organization — securing it but not slowing it down. The days of security as the team of “no” are no more.
As you consider the “people” piece of the data security puzzle, Laminar Security can equip your team with the right “process” and “technology” for success. We offer a data security posture management (DSPM) solution that gives a data security expert (or COE) the resources they need to respond to today’s challenges. Our platform can:
To learn more, check out Laminar’s in-depth DSPM guide and additional resources about the unique challenges and opportunities of protecting data in the cloud.
Get notified when a new piece is out